"Urgent: Your Meta Business Account Has Been Restricted" - Email Scam!
Beware of the Fake Meta (Facebook) Email Scam: "Urgent: Your Business Account Has Been Restricted"
Online scams have become increasingly sophisticated and prevalent in today's digital age. One scam targeting users of the popular social media platform Meta is the "Urgent: Your Meta Business Account Has Been Restricted" email scam. This phishing scam tricks recipients into clicking on a fake link and entering their login credentials or other sensitive information, which scammers can then use for fraudulent purposes. In this article, we will discuss what the "Urgent: Your Meta Business Account Has Been Restricted" email scam is, how it works, and what you can do to protect yourself from falling victim to this and other similar phishing scams.
Business Account Restricted
We regret to inform you that we have recently detected possible instances of copyright infringement on one or more pages linked to your business account. As a responsible platform, we take intellectual property rights very seriously and it is our obligation to ensure that all content posted by our users is in compliance with our policies and guidelines.
In order to conduct a thorough review of your case, we have temporarily limited your business account. We kindly request that you submit an appeal through our Business Help Center using the button provided below. It is important that your appeal contains all relevant information regarding the pages in question, as well as the origin of the content.
Should further information be required, we will contact you directly. We appreciate your cooperation and understanding throughout this process.
Please be advised that failure to respond within the specified timeframe may result in further action being taken, including permanent suspension or deletion of your business account for repeated violations.
Sincerely,
Bobby P.
What you can do
[ Do not click on this link - if you hover over the link REQUEST REVIEW it will be some unknown address]
What is the “Urgent: Your Meta Business Account Has Been Restricted” email?
The "Urgent: Your Meta Business Account Has Been Restricted" email scam is a phishing scam that targets users of the social media platform Meta (formerly known as Facebook). The scam email typically claims that the recipient's Meta Business Account has been restricted due to suspicious activity or a violation of the platform's terms of service, and urges the recipient to click on a link to verify their account information and avoid further restrictions.
However, the link provided in the email is fake and leads to a phishing website that is designed to steal the recipient's Meta login credentials, credit card information, or other sensitive data. Once the scammers obtain this information, they can use it to steal money or commit identity theft.
To avoid falling victim to this or similar scams, it's important to be cautious when receiving unsolicited emails, especially if they ask you to click on a link or provide sensitive information. Always double-check the sender's email address and hover over any links to make sure they lead to legitimate websites before clicking on them. It's also a good idea to enable two-factor authentication and use strong, unique passwords for all your online accounts.
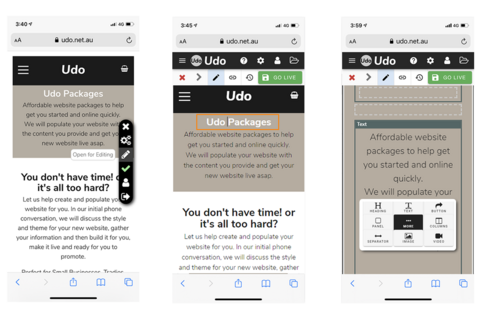
U do Web Builder
The first true CMS Mobile Editing.
"No App needed"
Easily update your website directly on your phone, update text, upload images, add products plus more...
Why do these scams happen?
Delving into the dark world of deceit, a burning question arises: why do scams thrive and continue to deceive unsuspecting victims? From the lure of easy money to the enticing prospect of a luxurious lifestyle, unravelling the psychological complexities behind these fraudulent schemes is a challenging and fascinating endeavour.
Let's explore the multifaceted world of scams and uncover the motivations driving these criminal activities.
Scams are fraudulent schemes that are designed to deceive individuals or organizations into giving up their money or sensitive information. There are many different types of scams, ranging from email phishing and online dating scams to investment scams and pyramid schemes. While the specific tactics used by scammers may differ, their motivations can generally be boiled down to a few key factors.
One of the main motivations driving scammers is financial gain. Many scams are designed to extract money from unsuspecting victims, either by convincing them to make a payment upfront for a promised service or product that never materializes, or by tricking them into giving up their bank account information or other sensitive financial information. In some cases, scammers may also use identity theft to access an individual's credit cards, bank accounts, or other financial assets.
Another motivation driving scammers is the desire for power and control. Some scammers derive pleasure from manipulating others and exploiting their vulnerabilities. They may use psychological tricks and emotional manipulation to gain the trust of their victims and convince them to do things they wouldn't normally do. In some cases, scammers may also use threats or intimidation to control their victims and prevent them from reporting the scam to the authorities.
Finally, some scammers are motivated by a desire for revenge or retaliation. They may seek to hurt others by spreading false information or defrauding them out of their money. In some cases, scammers may also be motivated by a desire for attention or notoriety, and they may use their scams as a way to gain recognition or admiration from others.
Regardless of the specific motivations driving scammers, it is important to remain vigilant and protect yourself against fraudulent schemes. This may include staying up-to-date on the latest types of scams, being cautious when giving out personal information, and reporting suspicious activity to the authorities.
Affordable Website Packages
5 stages of a scam.
While the specifics of a scam may vary, there are typically five stages that most scams follow. These stages are:
The setup: In this stage, the scammer sets the groundwork for the scam. They may create a fake website or social media profile, send a phishing email, or use some other method to make initial contact with the victim.
The hook: Once contact has been made, the scammer will typically use some kind of hook to get the victim interested. This might involve offering a too-good-to-be-true investment opportunity, promising a big payout for a small upfront payment, or using emotional manipulation to gain the victim's trust.
The buildup: In this stage, the scammer will continue to build up the victim's interest and trust. They may send fake documents or testimonials, make phone calls or send messages to answer any questions or concerns the victim may have, or even set up a fake office or storefront to make the scam seem more legitimate.
The request: Once the victim has been hooked and their trust has been gained, the scammer will make their request. This might involve asking for a large sum of money upfront, requesting access to the victim's bank account or other sensitive information, or asking the victim to take some other action that will benefit the scammer.
The takedown: In the final stage, the scammer will disappear with the victim's money or information. They may cut off all contact with the victim, delete their fake website or social media profile, or take other steps to avoid detection.
It is important to note that not all scams follow this exact sequence, and some may skip or combine certain stages. However, understanding these stages can help individuals recognize and avoid potential scams.
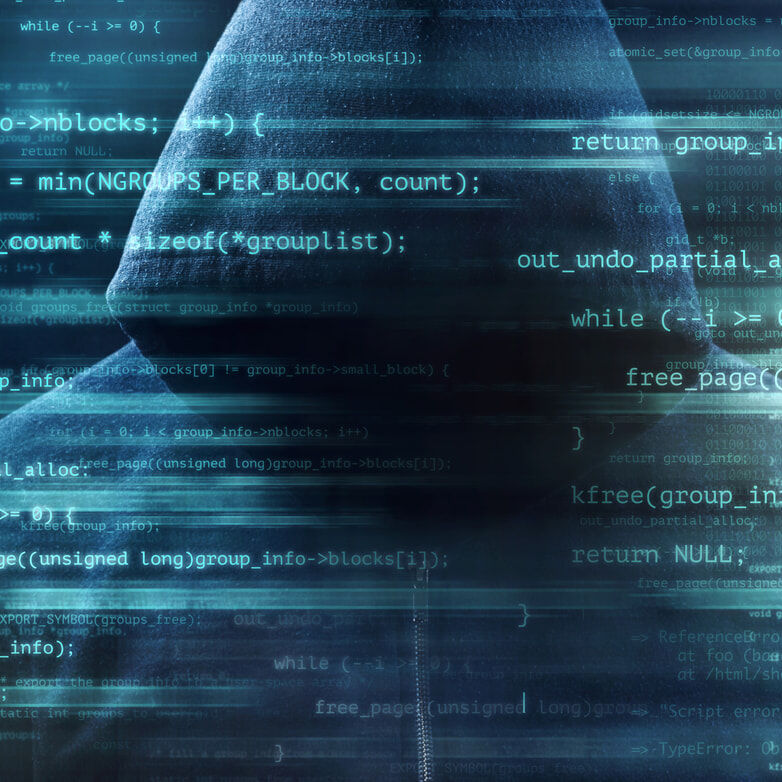
If you were hacked it's already too late.
In this case, If you have already been hacked or clicked on the link they provided and logged into their system, we highly recommend you take immediate action and contact Meta and inform them of what has happened to your account. We would suggest if you have credit card information attached to the account, delete them straight away though this may already be too late, contact your bank and make sure they're aware of the situation, and ask them what you should or can do to protect your accounts or perhaps cancel your cards and request new ones.
Don't wait until it's too late to take action if you've been hacked - these cyber-criminals aren't going to stop just because you pay their ransom. It's time to cut your losses, shut down, and start fresh with stronger security measures in place. Take this experience as a lesson and ensure you're better prepared for future threats.
Perhaps it's time to do a self-audit on all your security systems and check that passwords are strong for all your systems. Remember your security is only as good as your weakest password.
What do we mean by the weakest password!
A weak password is a password that is easy to guess or crack, and therefore provides little protection against unauthorized access to a user's account or sensitive information. Weak passwords are often simple, common, or easily guessable phrases or words, such as "password" or "123456."
A weak password may also be too short or lacks complexity, such as a password that only consists of lowercase letters or does not include numbers, symbols, or a mix of uppercase and lowercase letters.
Using weak passwords makes it easier for attackers to access user accounts and steal sensitive information, such as personal or financial information. It is important to use strong, unique passwords that are difficult for attackers to guess or crack. This can be achieved by using a combination of upper and lower case letters, numbers, and symbols and avoiding easily guessable words or phrases. It is also recommended to use a different password for each account, to minimize the impact of a potential breach.
What is a good password?
A good password is a strong, unique, and complex combination of letters, numbers, symbols, and uppercase and lowercase characters that is difficult to guess or crack. A good password should ideally be at least 16+ characters long, although longer passwords are even better.
Here are some tips for creating a good password:
Use a mix of characters: Use a combination of uppercase and lowercase letters, numbers, and symbols to make your password more complex and difficult to guess.
Avoid common phrases or words: Avoid using common phrases or words, such as "password" or "123456," as these are easily guessable.
Use a passphrase: Consider using a passphrase, which is a series of words or a sentence, rather than a single word. Passphrases can be easier to remember and harder to crack than traditional passwords.
Avoid using personal information: Do not use personal information such as your name, birth date, or other easily identifiable information in your password.
Use a unique password for each account: Avoid using the same password across multiple accounts, as this can increase the risk of a security breach.
Remember, creating a strong password is just one step in protecting your online accounts and personal information. It is also important to keep your software and devices up-to-date with the latest security patches and to use two-factor authentication whenever possible to provide an additional layer of security.
We highly recommend using 4 or 5-word phrases joined by hyphens that mean something to you so you can easily remember, however, keep in mind not commonly known words about you.
Example: create-technology-mouse-outcome
Perhaps use a password generator to create the ultimate password or perhaps use a password storage app like Bitwarden or 1Password especially if you have many passwords to keep track of.
Some final tips
Finally, if you get an email like this don't panic, the chances are it is a scam and is not true. The best advice we can give you is to not respond and ignore it completely.
We also recommend that you back up your website and store this in a secure offsite environment regularly just in case, this means if you were hacked or something else has happened to your website you will be able to restore an older version of the website with minimal impact.
Although this may add extra to the running costs of your website think about how much time and money would it cost if you were to lose everything and had to start again from scratch.